- Isolation of operating system.
- It refers to the process of using software to create a virtual resource that runs on a layer separate from the physical hardware. The most common use case of virtualization is cloud computing.
- In this process we create a virtual computer having existence of hardware and runs on a VM with some specifications such as Memory.
- Isolation of an application.
- Containerization is the process of packaging every component needed to run an application or microservice, including associated libraries. Each container consists of codes, dependencies, and the OS itself. It allows applications to run the same way on multiple platforms.
| Virtualsation | Containerization |
|---|---|
| Virtualization aims to run multiple OS instance on a single server | Whereas Containerization runs a single OS instance |
- Onion architecture consists of several concentric layers interacting with each other towards the core, which is the domain. The architecture does not depend on the data layer, as in a traditional three-tier architecture; it depends on real domain models.
- Data Access Layer — responsible for data processing
- Business Logic Layer — responsible for app logic
- Presentation Layer — responsible for the display (UI, Web API).
-
The main problem with this architecture is that all layers are built on top of the Data Access Layer and are, in fact, tied to a certain type of data storage. If this type changes, it causes changes at all levels. The Entity Framework partially solves this problem, but it supports a limited number of database types.
-
With onion architecture, there is only an object model at the lowest level, which does not depend on the type of database. The actual type of database and the way of storing data is determined at the upper infrastructure level.
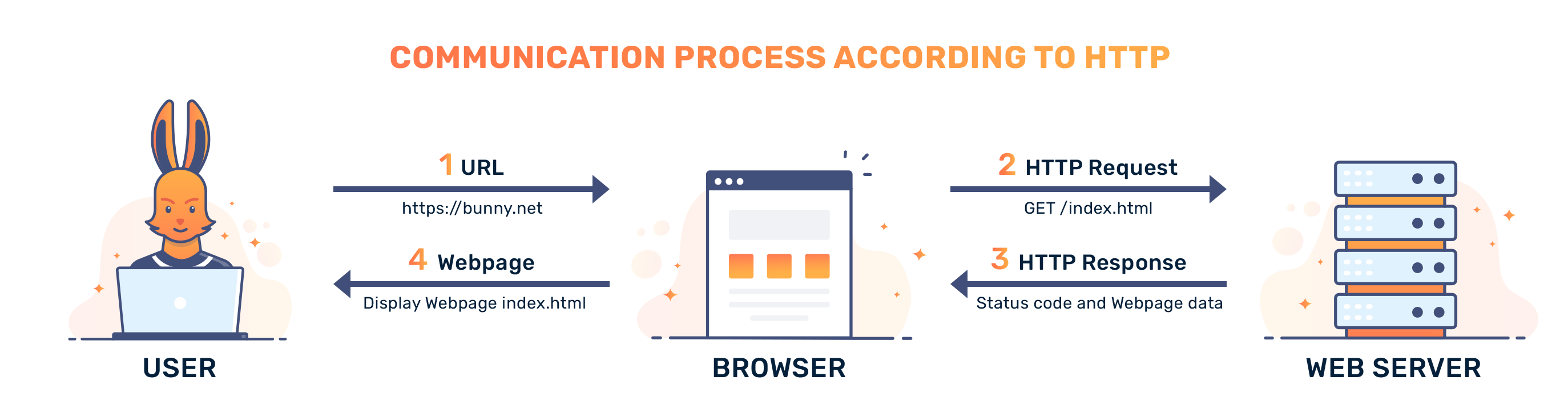
- HTTP stands for HyperText Transfer Language.
- HTTP is a protocol whhich allows the fetching of rersources, such as HTML documents.
- It is the foundation of any data exchange on the web.
- It is a client-server Protocol, which means request is initiated by the recipient, usually the web browser.
- A complete document is reconstructed from the different-sub document fetched, for instance text, layout description, image videos, scruipts and more.
- Some other resources
- https://en.wikipedia.org/wiki/Man-in-the-middle_attack
- https://developer.mozilla.org/en-US/docs/Web/HTTP/Methods
- https://developer.mozilla.org/en-US/docs/Web/HTTP/Status
- https://www.imperva.com/learn/application-security/osi-model/
- Session
- Infrastructure
- IP address
- DNS
- Session
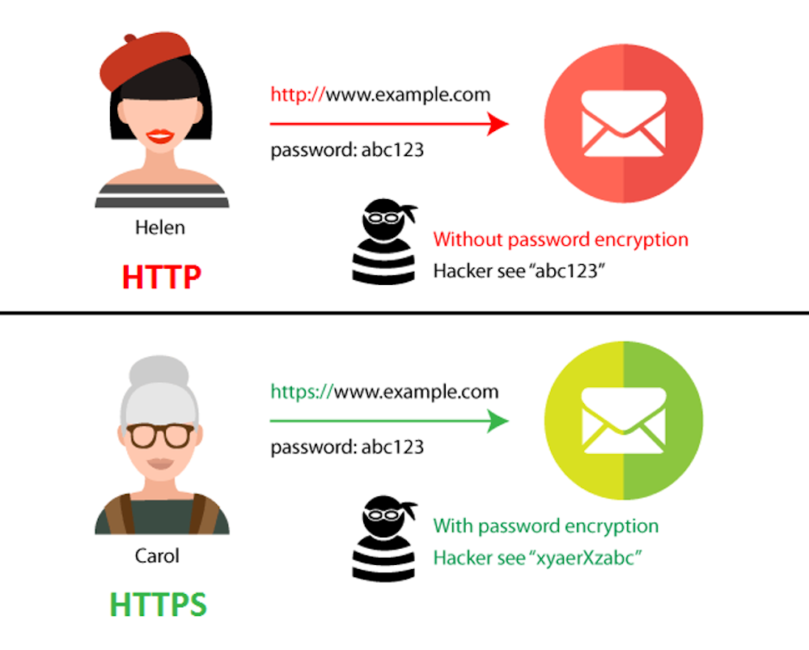
- HTTP, HTTPS
- Networking: OSI Model
- DNS
- SSL