API service for accessing the Mail.Baby services.
Sample clients for the API are available in many languages
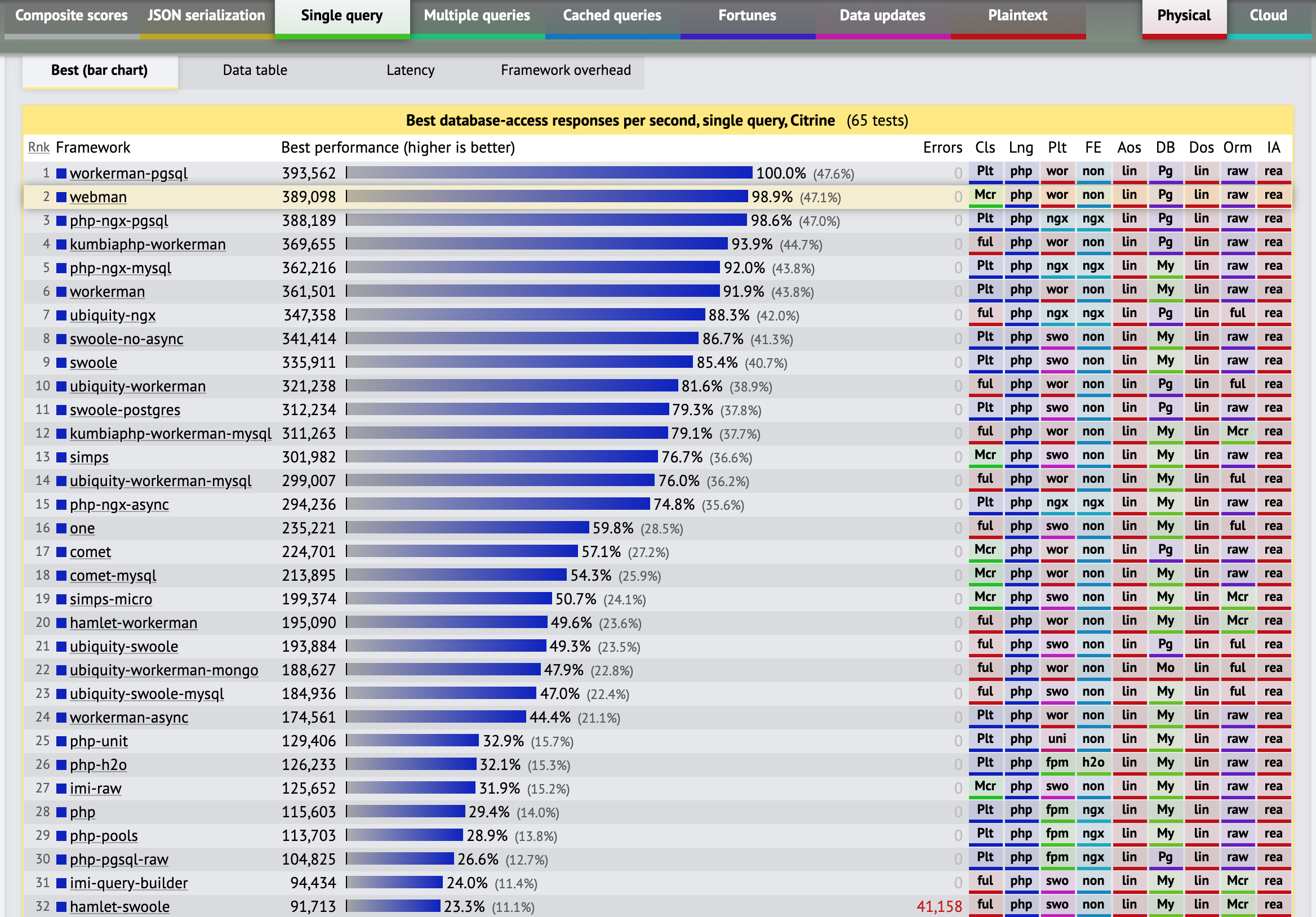
This is built on top of Webman, a high performance HTTP Service Framework for PHP based on Workerman.
We are utilizing the OpenAPI (formerly known as Swagger) spec for this API. It is basically the next evolution of SOAP API's with well defined functions, parameters, and responses. While there are many editors out there I'm currently using SwaggerHub to do most of the editing of the spec.
After testing every PHP library out there dealing with concurrent/asynchronous processing many times over the years I've found Workerman to be the overall best. It has proven more stable and by far faster than the alternatives with the one big downside being that its documentation and code comments are all in Chinese. Webman is a fairly recently created web framework on top of Workerman. There had been many previously created frameworks based on workerman and while some were good Webman seemed to hit that perfect balance between ease-of-use and power.
The Chinese documentation is easily readable Using either the auto translate in Chrome or an addon like Translate Web Pages for Firefox.
- WebMan Manual WebMan framework documentation
- Illuminate Database Docs
- StopLight Elements OpenAPI Documentor
- MailBaby Swagger-UI
- MailBaby generator HTML2 Docs
- MailBaby generated PHP Client PHP Client generated by the OpenAPI Generator/Swagger Codegen
- Redoc - OpenAPI/Swagger-generated API Reference Documentation
- RapiDoc - Custom-Element for OpenAPI Spec
- OpenDocumenter is a automatic documentation generator for OpenAPI v3 schemas. Simply provide your schema file in JSON or YAML, then sit back and enjoy the documentation.
- OpenAPI Explorer - OpenAPI Web component to generate a UI from the spec.
- oas3-api-snippet-enricher Enrich your OpenAPI 3.0 JSON with code samples
- OpenAPI-Viewer - OpenApi viewer Implemented using Vue
- LucyBot Documentation Starter - Interactive REST API Documentation
Building Elements:
git clone [email protected]:stoplightio/elements.git
cd elements
sed s#"\"httpsnippet\".*$"#"\"httpsnippet\": \"detain/httpsnippet\#master\","#g -i packages/elements-core/package.json
src="https://raw.githubusercontent.com/stoplightio/Public-APIs/master/reference/zoom/openapi.yaml"
dst="https://raw.githubusercontent.com/interserver/mailbaby-mail-api/master/public/spec/openapi.yaml"
for i in examples/angular/src/app/api/api.component.ts examples/react-gatsby/src/pages/zoom-api.tsx examples/react-cra/src/components/API.tsx; do
sed s#"${src}"#"${dst}"#g -i $i
done
sed s#"https://api.apis.guru/v2/specs/github.com/1.1.4/openapi.yaml"#"${dst}"#g -i examples/bootstrap/index.html
yarn
yarn build
yarn build:angular
yarn build:react-gatsby
yarn build:react-cra
- Customize 404 Page
- Testing
- Additional error checking and handling
- Auto Updates
- Placing Orders
- OpenAPI Tools Listing of OpenAPI relatd tools by category (Documentors, Parsers, Mockers, etc)
- OpenAPI PSR-7 Message Validator
- PHPMailer email sending library for PHP
- Swagger UI
- Swagger Editor
- OpenAPI GUI
https://www.techempower.com/benchmarks/#section=test&runid=9716e3cd-9e53-433c-b6c5-d2c48c9593c1&hw=ph&test=db&l=zg24n3-1r&a=2